What is Quantum Cryptography and How Will it Help the Future of Security? Part 1
The world of cyber-security is changing, and with the invention of quantum computers, much of our current encryption software and safeguards are useless. There are new safeguards; however, that is being created to help prevent hackers and other busybodies from accessing data that they have no business seeing. Quantum Key Distribution, QKD, can detect hackers and attempts to snoop at the second they occur and shut them down effectively. Quantum cryptography essentially uses physics to create a secure cryptosystem between the sender and receiver without having the message compromised by a third party or potential hacker.
How Does Quantum Key Distribution Work?
QKD works to help make sure that no one can hack into the system as information is being transmitted by attaching directly to the cable. The QKD sender works to transmit photons down fiber, the photons are sent one at a time to the receiver. Each photon is assigned one polarization, phase, or position that helps to designate if that photon is going to be a 1 or a 0 in the binary system.
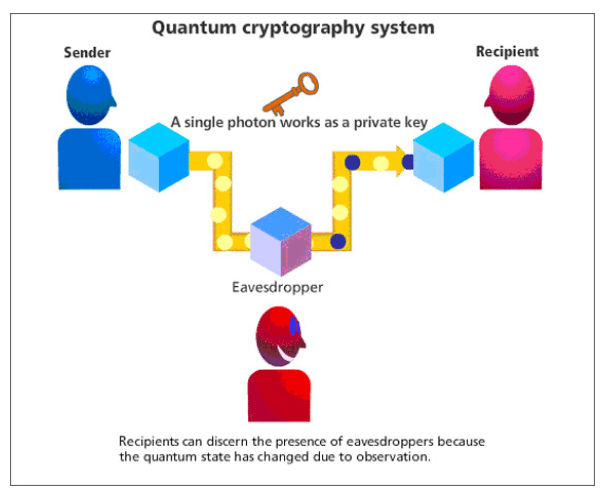
When the data is sent, these photons can be 1 and 0 at the same time. QKD works so that when these photons are stopped and observed, they become fixed. This makes it so that when the data is then sent to the receiver, it is nothing but garbled and jumbled nonsense. This means that the hack is apparent immediately so that the receiver can alert the sender that the line is being tapped and accessed when it should not be.
This allows for quick, nearly immediate, knowledge that the line is being observed and that transmissions need to be stopped so that no more data is corrupted or intercepted. This means that when the line is tapped or when it becomes apparent that the information is compromised, it can be stopped so that no more information is transmitted. Nothing else is changed or accessed without permission for this mission-critical communication.
In our next blog, we outline the specifics concerning whether quantum cryptography is useful and how, exactly, adequate data encryption is achieved. Data encryption, reliability and security remains at the forefront of mission critical uses, which can include uses from the U.S. military, first responders, Government and more. For more information about cyber security, secure mobile VPN and more, click here.


No Comments
Sorry, the comment form is closed at this time.